Configuring HTTP Header Proxy Authentication¶
Introduction¶
Proxy authentication is used in multi-tier system. The user/principal authenticates at the proxy and the proxy provides the authentication information to other services.
This tutorial shows how to configure GeoServer to accept authentication information passed by HTTP header attribute(s). In this scenario GeoServer will do no actual authentication itself.
Prerequisites¶
This tutorial uses the curl utility to issue HTTP request that test authentication. Install curl before proceeding.
Note
Any utility that supports setting HTTP header attributes can be used in place of curl.
Configure the HTTP header filter¶
-
Start GeoServer and login to the web admin interface as the
adminuser. -
Click the
Authenticationlink located under theSecuritysection of the navigation sidebar.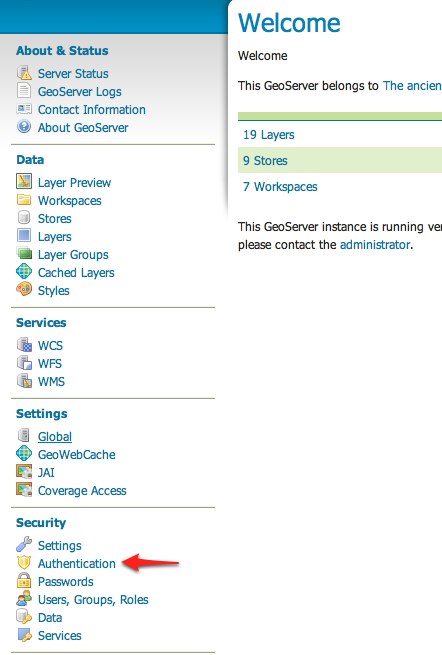
-
Scroll down to the
Authentication Filterspanel and click theAdd newlink.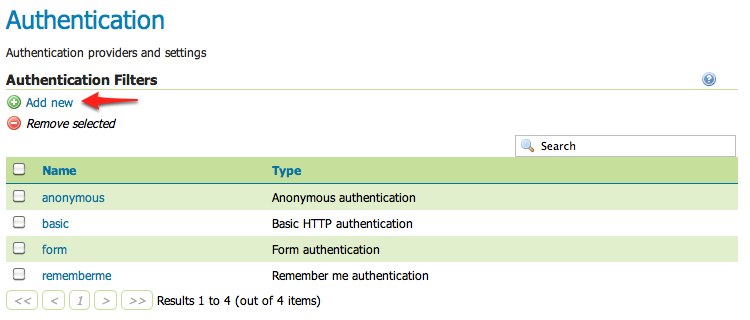
-
Click the
HTTP Headerlink.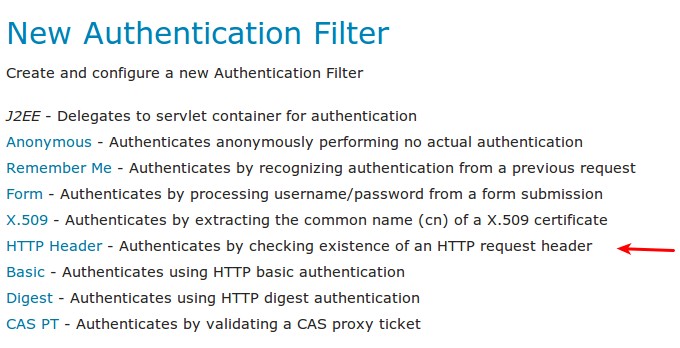
-
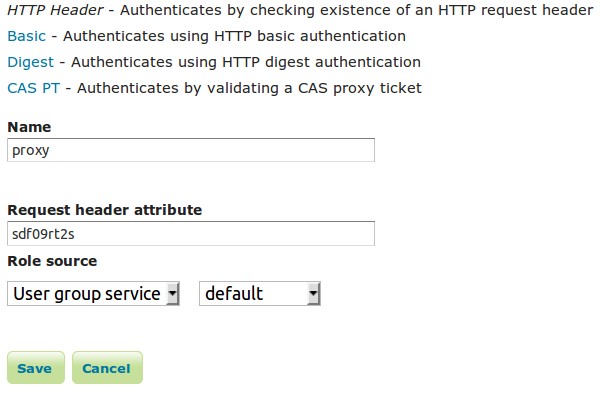
Fill in the fields of the settings form as follows:
- Set
Nameto "proxy" - Set
Request header attributeto "sdf09rt2s" - Set
Role sourceto "User group service" - Set the name of the user group service to "default"
- Set
Additional information about role services is here Role source and role calculation
Warning
The tutorial uses the obscure "sdf09rt2s" name for the header attribute. Why not use "user" or "username" ?. In a proxy scenario a relationship of trust is needed between the proxy and GeoServer. An attacker could easily send an HTTP request with an HTTP header attribute "user" and value "admin" and operate as an administrator.
One possibility is to configure the network infrastructure preventing such requests from all IP addresses except the IP of the proxy.
This tutorial uses a obscure header attribute name which should be a shared secret between the proxy and GeoServer. Additionally, the use of SSL is recommended, otherwise the shared secret is transported in plain text.
-
Save.
-
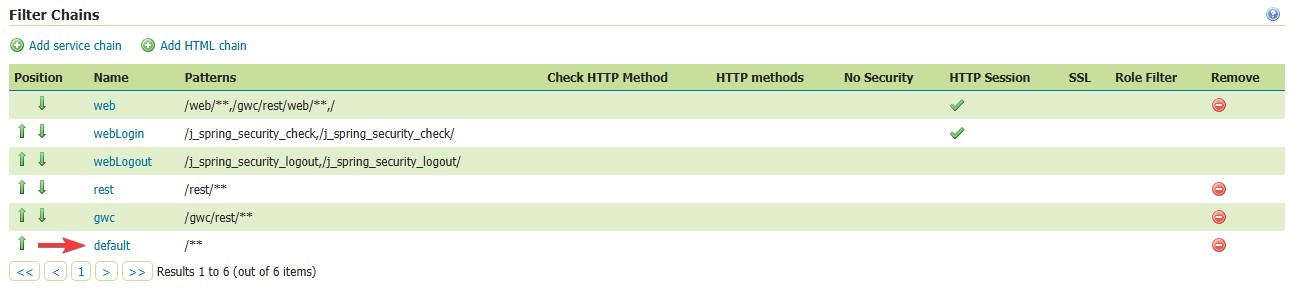
Back on the authentication page scroll down to the
Filter Chainspanel. -
Select "Default" from the list of filter chains.
-
Scroll down to the
Chain filterssection and unselect thebasicfilter and select theproxyfilter. Position the theproxyfilter before theanonymousfilter.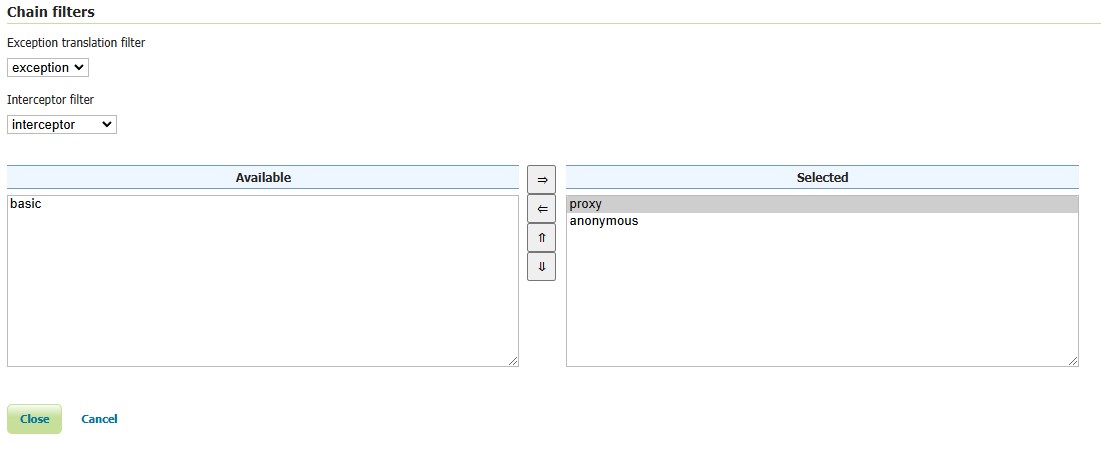
-
Click close at the bottom of the page and then click Save back on the Authentication page to save your filter chain changes.
Secure OGC service requests¶
In order to test the authentication settings configured in the previous section a service or resource must be first secured. The Default filter chain is the chain applied to all OGC service requests so a service security rule must be configured.
-
From the GeoServer home page and click the
Serviceslink located under theSecuritysection of the navigation sidebar.
-
On the Service security page click the
Add new rulelink and add a catch all rule that secures all OGC service requests requiring theADMINrole.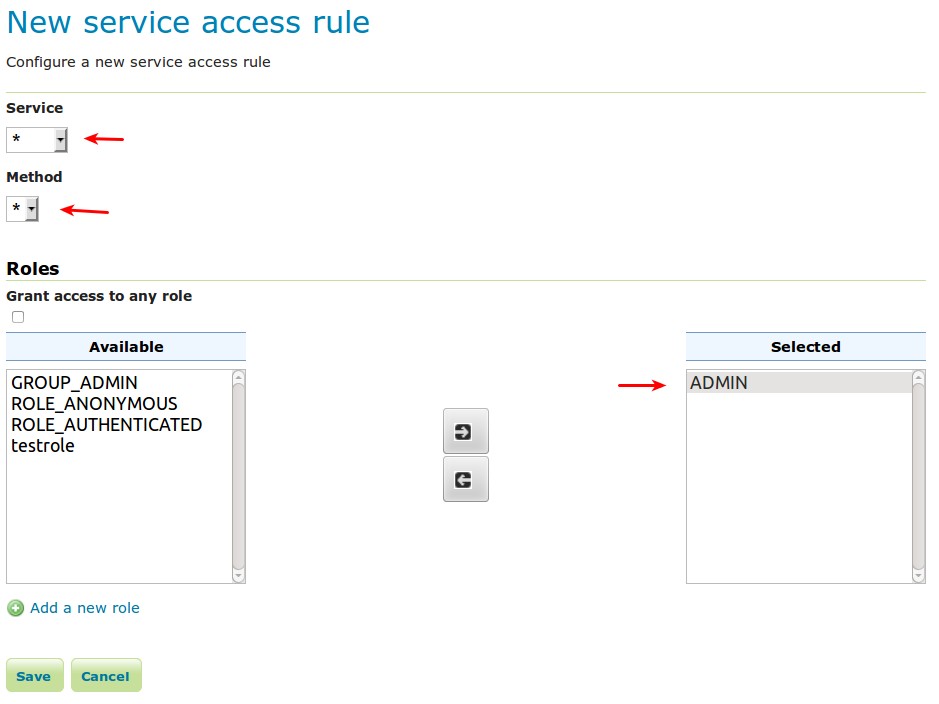
-
Save.
Test a proxy login¶
-
Execute the following curl command:
The result should be a 403 response signaling that access is denied. The output should look something like the following:
* About to connect() to localhost port 8080 (#0)
* Trying ::1... connected
> GET /geoserver/wfs?request=getcapabilities HTTP/1.1
> User-Agent: curl/7.22.0 (x86_64-pc-linux-gnu) libcurl/7.22.0 OpenSSL/1.0.1 zlib/1.2.3.4 libidn/1.23 librtmp/2.3
> Host: localhost:8080
> Accept: */*
>
< HTTP/1.1 403 Access Denied
< Content-Type: text/html; charset=iso-8859-1
< Content-Length: 1407
< Server: Jetty(6.1.8)
<
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=ISO-8859-1"/>
<title>Error 403 Access Denied</title>
</head>
...
-
Execute the same command but specify the
--headeroption.:curl -v --header "sdf09rt2s: admin" -G "http://localhost:8080/geoserver/wfs?request=getcapabilities"The result should be a successful authentication and contain the normal WFS capabilities response.
Note
When setting the header
name: valuepair, the headernameshould match theRequest Header Attributethat was set when creating the new Authentication Filter, and thevaluemust match the username for a user who has the correct Role set. The username value is case sensitive.In the above example, the
adminuser is assigned to theADMINrole which is the role that was selected in the service rule we created. If you had a different user that was assigned to theADMINrole, you could instead use the username for that user as thevaluein the header and you should get the correct capabilities response.